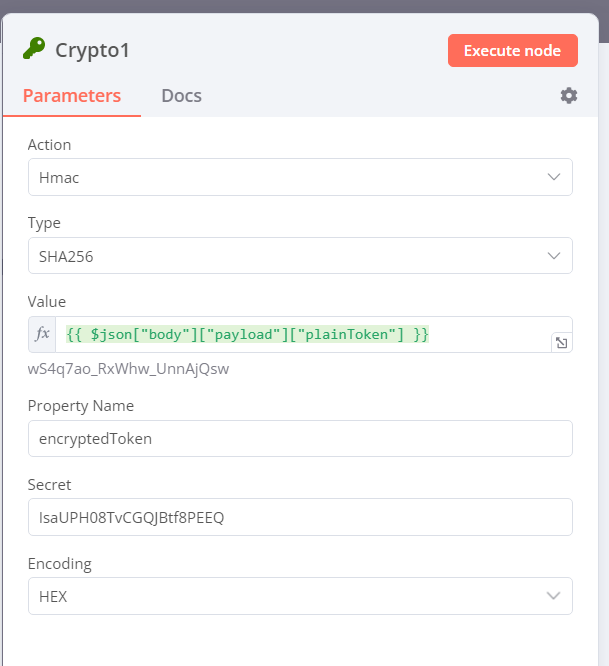
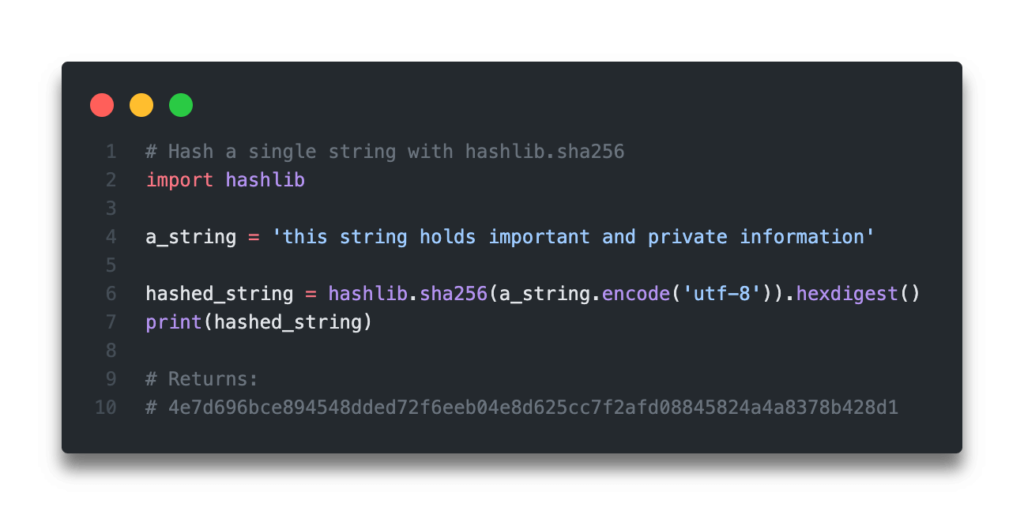
SHA 256: Compute a SHA 256 hash using C# for effective security - .Net Core | MVC | HTML Agility Pack | SQL | Technology Crowds

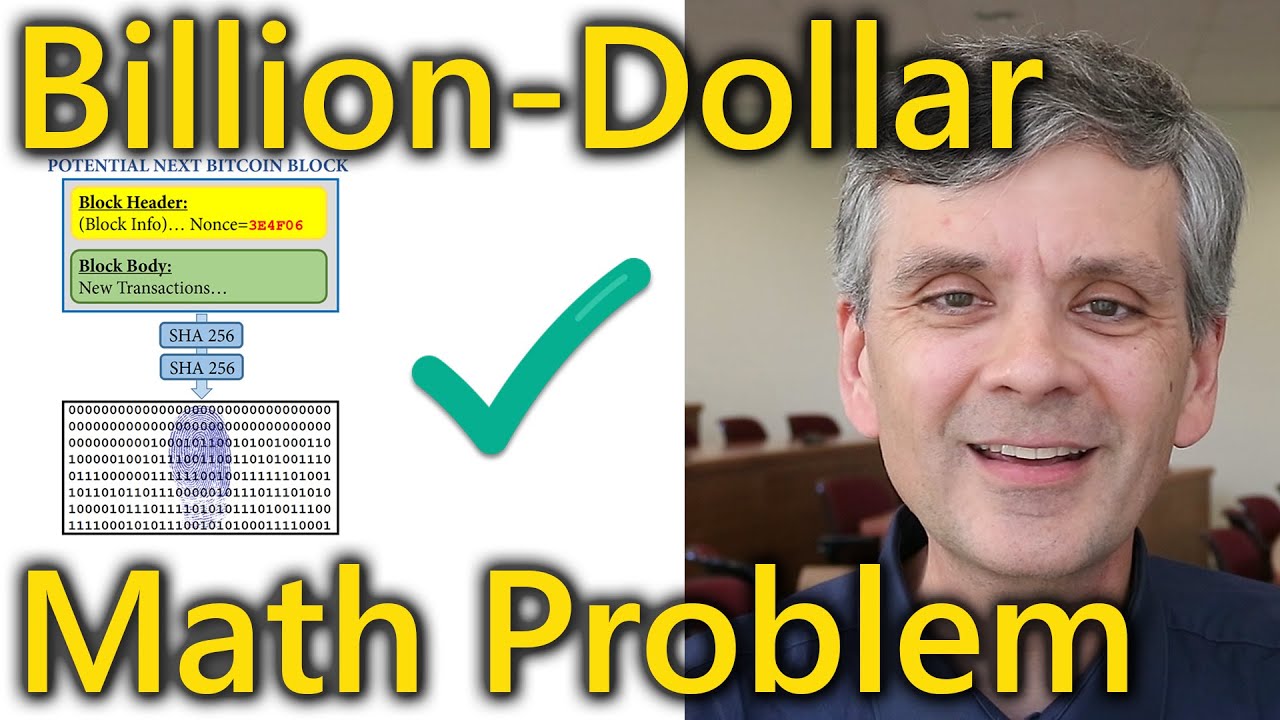
Comparing Blake3 and SHA-256 Data Integrity Algorithms & Integrating Blake3 with Golang | by Baran KİBAR | Stackademic